Threat Intelligence Fundamentals

Threat Intelligence Fundamentals — My Learning Journey with HTB
my first real step into CTI
As a cybersecurity student, I’ve always been fascinated by how defenders stay ahead of attackers. But honestly, “threat intelligence” used to sound like a buzzword something only senior analysts or big security teams worried about.
That changed when I worked through the Threat Intelligence Fundamentals module on Hack The Box (HTB). It gave me a clear, hands-on look at what CTI actually means, why it matters, and how it connects directly to the day-to-day work I want to do as a SOC analyst.
Building my foundation — the four pillars
One of the first lessons HTB drilled into me was that not all intelligence is created equal. The module introduced the four qualities that make CTI useful:
- Relevance: If it doesn’t apply to my environment, it’s noise.
- Timeliness: Intel has a shelf life; outdated IOCs are dead weight.
- Actionability: If it doesn’t guide action, it’s just trivia.
- Accuracy: False positives can waste hours or even break systems.
This simple checklist reshaped how I think about every piece of intel. Even as a student, I started asking: “Can I use this? And is it worth my time?”
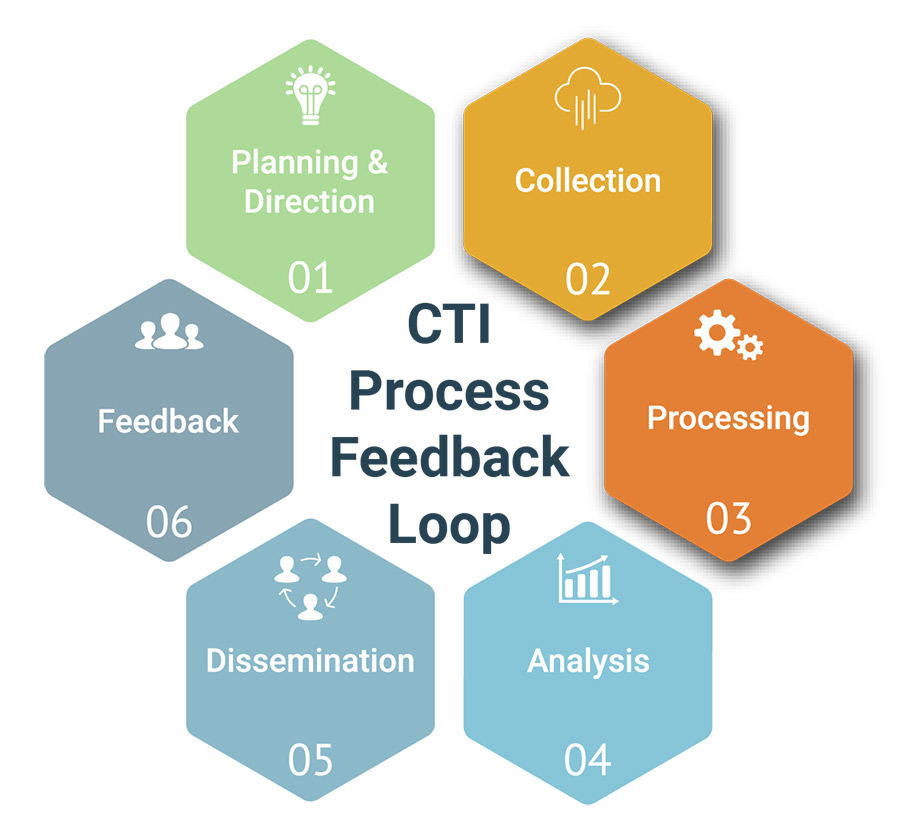
The levels of CTI — strategic, operational, tactical
Before this module, I used to lump all cyber intel into one bucket. HTB broke it down into three layers, each serving different purposes:
- Strategic intel helps leadership see the bigger picture of who’s attacking and why.
- Operational intel gives SOC teams direction by explaining attacker campaigns and methods.
- Tactical intel provides the raw IOCs the hashes, domains, and behaviors that we can hunt for.
As a student preparing for real SOC work, I realized that tactical and operational levels are my playground. That’s where the real detection, hunting, and triage happen.
Intelligence vs. hunting
Another “aha” moment came when HTB explained the difference between threat intelligence and threat hunting:
- CTI predicts what adversaries are likely to do.
- Hunting investigates whether they’re already active in the system.
That clicked for me: intel fuels the hunt, and the hunt improves intel. It’s a cycle. Before this module, I thought they were separate tasks — now I see how closely they depend on each other.
My personal lightbulb moment
What stood out most was how structured intelligence actually is. As a student, I used to skim threat reports and just copy IOCs. But HTB taught me to treat reports like stories about the adversary.
- Beginning: How they get in (phishing, exploits, stolen creds).
- Middle: How they move and act (PowerShell, lateral movement, persistence).
- End: What they try to achieve (exfiltration, ransomware, sabotage).
Reading intel this way made me realize: if I know the “storyline,” I can anticipate what the attacker might try next — and set up defenses in advance.
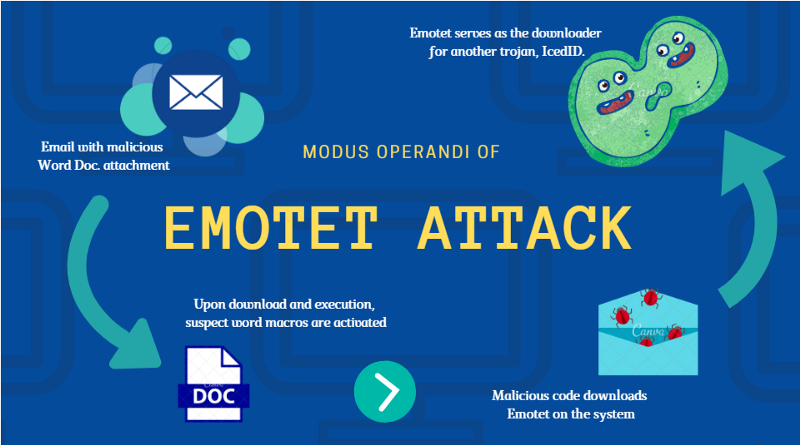
Case study — my Emotet walkthrough
The highlight of the module for me was working through Emotet as a real example. Here’s how I approached it:
- Understanding context: Emotet was targeting sectors similar to ours via phishing emails instantly relevant.
- Breaking down IOCs: I sorted them into network (IPs), host (hashes, registry keys), and email (senders, subject lines).
- Mapping to MITRE ATT&CK: Techniques like phishing (T1566), PowerShell execution (T1059), and persistence via registry keys came to life.
- Validating intel: Some IOCs were outdated — teaching me not to blindly trust every feed.
- Operationalizing intel: I imagined how I’d apply this in a SOC — updating SIEM rules, feeding indicators into EDR, and adjusting email filters.
- Threat hunting: I went beyond static IOCs, looking for suspicious behaviors like Word → PowerShell process chains or odd SMB traffic.
- Takeaway: Behaviors tell the bigger story, not just one-off indicators.
That case study gave me a real sense of how theory translates into practice.
My takeaways as a student
Here’s what I walked away with from HTB’s module:
- Not all intelligence is worth acting on relevance and timeliness matter most.
- Always validate IOCs before deploying them.
- Think in adversary stories, not just lists of data.
- Use MITRE ATT&CK to keep investigations structured.
- Intelligence and hunting feed each other in a loop.
Conclusion
For me, the Threat Intelligence Fundamentals module wasn’t just another step in my learning path. It felt like the moment I stopped seeing myself as “just a student” and started thinking like a future SOC analyst.
I now understand how CTI turns random data into something meaningful, and how it empowers defenders to be proactive instead of reactive. This perspective is going to guide me in every lab, project, and eventually in the SOC role I’m working toward.

When I first cracked open Splunk, I’ll be honest, it felt like staring into a black hole of data. Millions…
When I first got into cybersecurity, I thought most of it was about prevention ,building firewalls, patching systems, and running…