Project Intruduction
I built a hands-on detection for DLL hijacking using Sysmon (module load events). I modified a production-grade Sysmon config, generated telemetry for an intentional calc.exe DLL hijack, analyzed Event ID 7 (ImageLoaded), extracted IOCs, and created reliable detection logic that distinguishes benign loads from malicious hijacks.
Objective
Detect DLL hijacking (where an attacker places a malicious DLL next to a legitimate executable) by leveraging Sysmon module load events (Event ID 7), and produce actionable IOCs and detection rules suitable for SIEM ingestion.
Tools & Tech used
- Windows 10/11 test host (lab VM)
- Sysinternals Sysmon (v13+ recommended)
- SwiftOnSecurity sysmonconfig-export.xml (base config)
- A writable user directory (Desktop) to simulate hijack conditions
- Example reflective DLL (for PoC) — used only for demonstration
- Event Viewer (Microsoft-Windows-Sysmon/Operational)
1) Prep: baseline Sysmon config
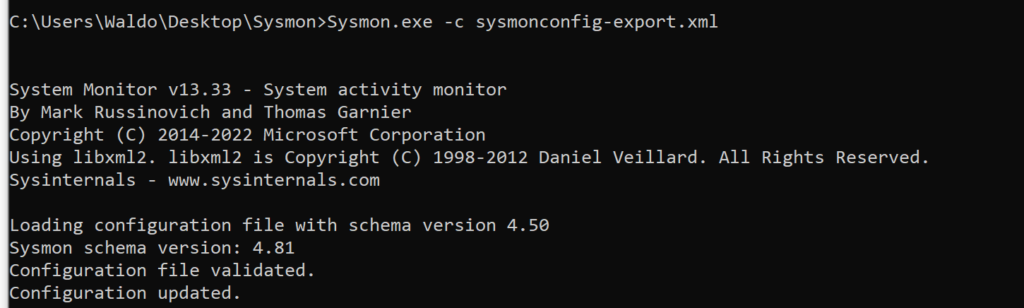
I downloaded the SwiftOnSecurity sysmonconfig-export.xml as a starting point and loaded it into Sysmon so we’d collect module load events.
Command used:
# Run as admin in C:\Tools\Sysmon or wherever sysmon.exe is located
.\sysmon.exe -c sysmonconfig-export.xml
Result: Sysmon validated and updated configuration and began logging ImageLoad events (Event ID 7).
2) Why Event ID 7?
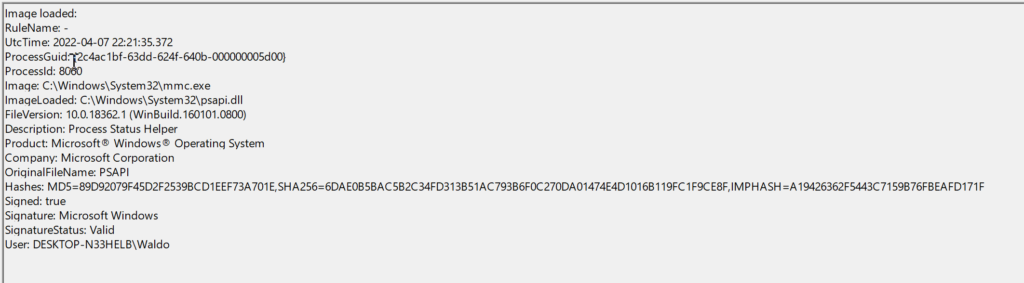
Sysmon Event ID 7 logs module (DLL) loads and includes fields such as:
- Image (the process/executable that loaded the DLL)
- ImageLoaded (DLL filename)
- Signed (signing status)
- User and ProcessID
This telemetry is perfect for detecting DLL hijacks where a process loads an unexpected, unsigned DLL from a writable path.
3) PoC: Perform a DLL hijack (lab-safe)
Now, I proceeded with building a detection mechanism. To gain more insights into DLL hijacks
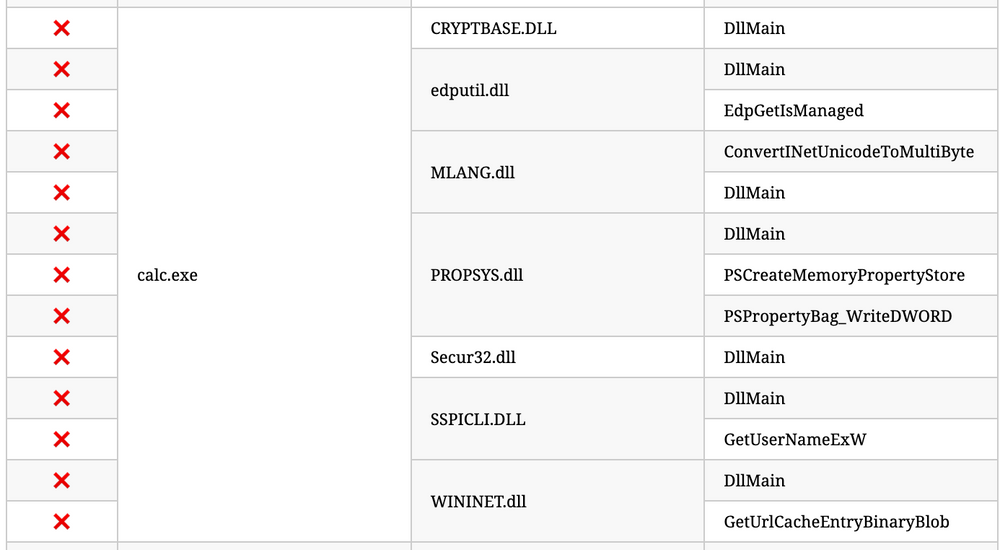
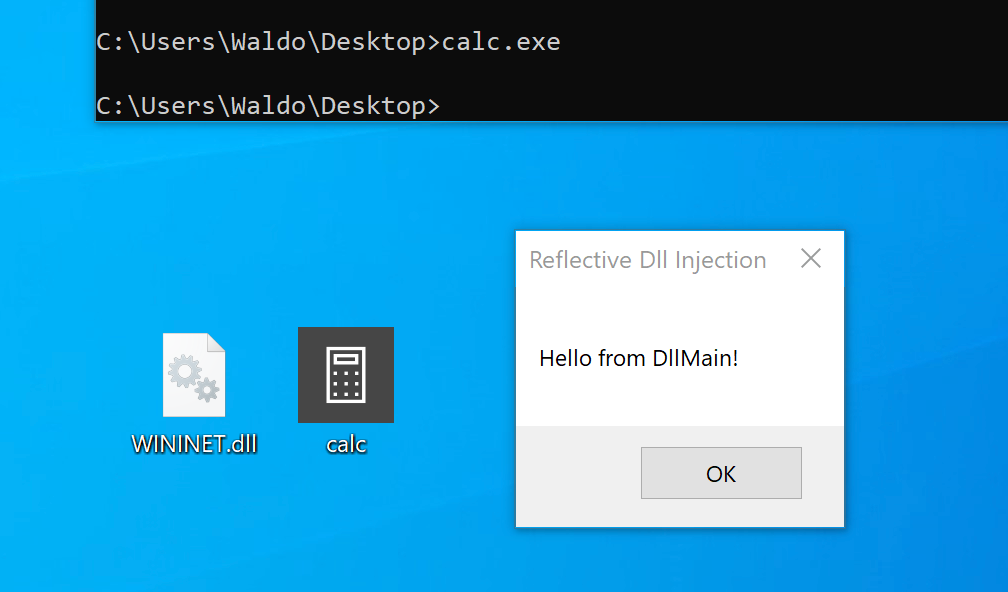
I simulated a hijack against calc.exe:
- Renamed a test reflective DLL to WININET.dll.
- Copied calc.exe and WININET.dll into a writable folder (Desktop).
- Executed the local calc.exe copy.
Outcome: Instead of the regular calculator, the injected DLL executed and showed a Hello from DllMain! messagebox — confirming the hijack worked.
Screenshot placeholders:
- screenshot-03-desktop-with-calc-dll.png — desktop showing calc.exe + WININET.dll
- screenshot-04-poc-popup.png — popup from injected DLL
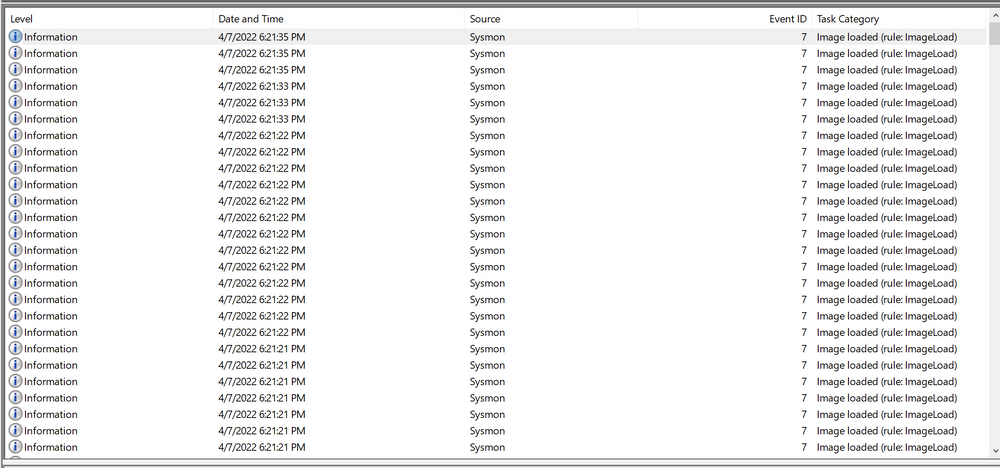
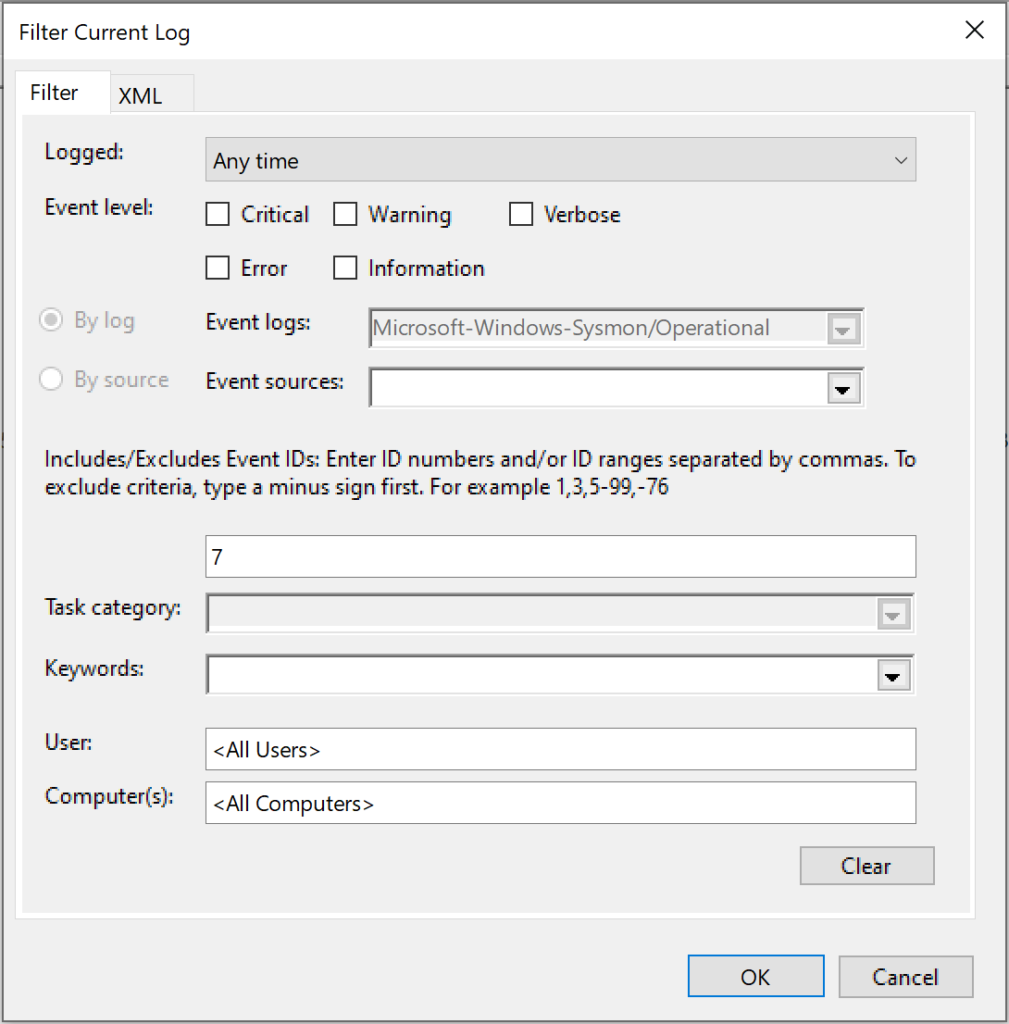
4) Analyze logs and derive IOCs
I filtered Sysmon logs for Event ID 7, then searched for calc.exe loads. I compared the malicious load vs normal system load:
Malicious PoC entry (example):
- Image: C:\Users\wd\Desktop\calc.exe
- ImageLoaded: WININET.dll
- Signed: false
Normal entry (system):
- Image: C:\Windows\System32\calc.exe
- ImageLoaded: wininet.dll
- Signed: true
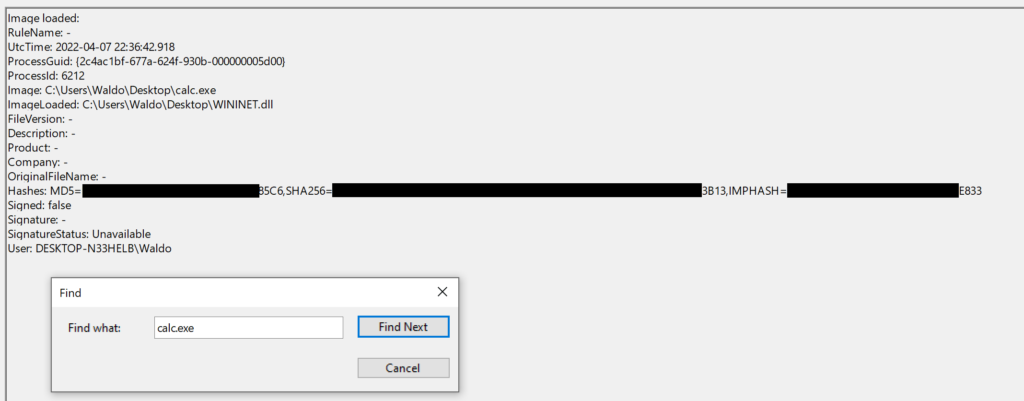
From this I derived consistent IOCs:
- calc.exe running from a writable/non-System32 path — should not happen in normal operations.
- WININET.dll (or other system DLL) loaded from non-System32 directory when parent process is a system binary — suspicious.
- Unsigned DLL where the legitimate DLL is signed.
This project showcased the full lifecycle of threat detection from understanding the attack (DLL hijacking), to simulating it in a controlled lab, then collecting telemetry with Sysmon, and finally building detection logic and practical remediation steps. By modifying Sysmon’s configuration to capture Event ID 7 and analyzing the resulting logs, I learned how attackers can exploit legitimate executables and how defenders can spot those anomalies.
The exercise reinforced three key lessons:
Telemetry matters having the right logging (Sysmon in this case) makes or breaks detection.
Context is everything combining process path, DLL signing, and file location drastically reduces false positives.
Detection is only half the battle pairing IOCs with remediation guidance ensures the findings are actionable in a real SOC.
Overall, this project not only deepened my technical skills with Windows internals and Sysmon but also demonstrated my ability to turn raw log data into real-world detection rules that could be deployed in an enterprise SIEM. It’s a clear example of how I can bridge the gap between offensive techniques and defensive monitoring in cybersecurity.